As Europe’s energy systems undergo rapid digital transformation, the intersection between cybersecurity and energy resilience has never been more critical. This Weekend Read explores how the continent’s shift towards smarter, decentralised, and data-driven energy infrastructure is creating both opportunities and vulnerabilities. It examines key technologies driving this change, reviews recent real-world cyber incidents — including several that took place in 2025 — and draws on research from The Voice of Renewables to highlight emerging trends, lessons, and strategies for strengthening Europe’s digital energy defences.
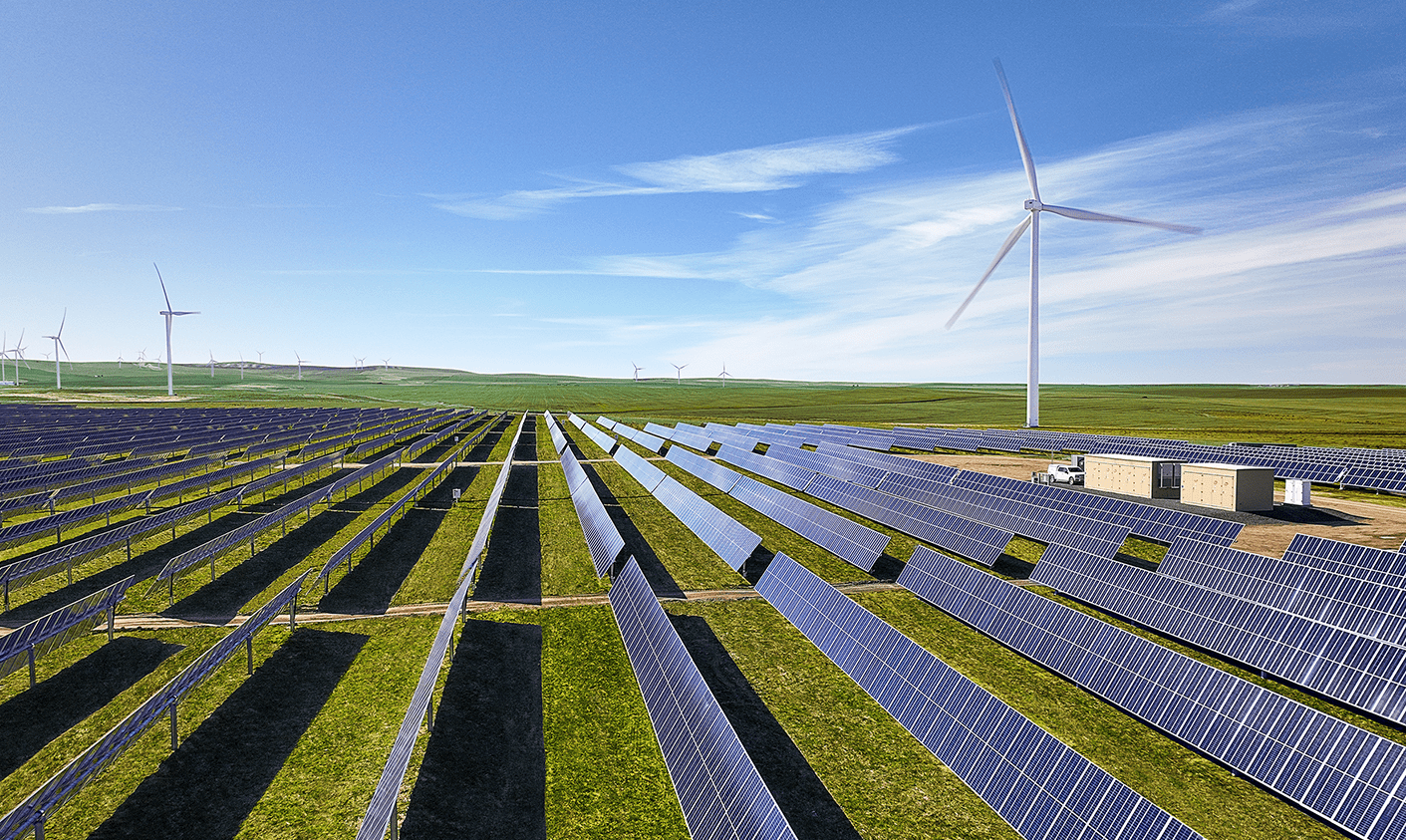
Europe’s energy landscape is evolving at an unprecedented pace. Driven by the imperatives of decarbonisation, decentralisation, and digitalisation, the continent’s power systems are becoming smarter, more interconnected, and increasingly reliant on digital technologies. This transformation is essential for integrating renewables, improving efficiency, and enhancing flexibility — but it also introduces new vulnerabilities. As information technology (IT) and operational technology (OT) systems converge, the energy sector’s exposure to cyber threats is growing, and so too is the need for robust and adaptive cybersecurity strategies.
Several emerging technologies are redefining Europe’s energy future. Digital twins — virtual replicas of physical infrastructure — enable operators to simulate scenarios, predict failures, and optimise asset use. Artificial intelligence (AI) and machine learning improve forecasting, automate decision-making, and detect anomalies before they escalate. Blockchain technologies are being tested to secure transactions, verify data integrity, and facilitate peer-to-peer energy trading. Meanwhile, flexibility services — such as demand response, battery storage, and virtual power plants — are critical to balancing intermittent renewable generation with real-time consumption.
These innovations bring immense benefits, but they also widen the attack surface of the energy ecosystem. Millions of new IoT devices — from smart meters to grid sensors — are now connected to critical networks, often with inconsistent or insufficient security standards. AI systems can be manipulated through data poisoning or adversarial attacks, and blockchain implementations face challenges of scalability and privacy. The growing digitalisation of flexibility services introduces further dependencies on real-time data flows, where any compromise could result in operational disruption or even cascading grid failures.
Europe has recognised these risks and is taking significant action. Regulatory measures such as the NIS2 Directive impose stricter cybersecurity obligations on operators of essential services, while initiatives like TwinEU are developing federated digital twins to enhance grid resilience and planning. The Common European Energy Data Space aims to standardise data governance and interoperability, and regular EU-wide exercises such as Cyber Europe test cross-border response readiness. Yet, despite this progress, recent real-world incidents show that vulnerabilities persist across both IT and OT environments.
Rising Threats: Lessons from Recent Cyber Incidents
The past two years have seen a notable increase in cyberattacks targeting Europe’s energy infrastructure. In December 2024, Romanian electricity distributor Electrica, serving nearly four million customers, was struck by a ransomware attack that crippled IT operations. Thanks to strong network segmentation, critical SCADA systems were spared — but the disruption caused substantial operational delays and financial losses. A year earlier, Slovenia’s largest power producer, HSE, experienced a similar ransomware breach, which forced temporary shutdowns of internal systems but avoided physical impact.
In 2025, however, incidents became more aggressive and complex:
- Norway’s Bremanger Dam Sabotage (April 2025) — Attackers allegedly manipulated digital controls to remotely open floodgates, releasing thousands of cubic metres of water and causing significant environmental and structural damage. Although attribution remains disputed, the case demonstrated how digital compromise can translate into physical harm.
- Iberian Peninsula Blackout (Spain and Portugal, April 2025) — A massive ten-hour blackout disrupted energy, transport, and telecommunications across the region. While investigations ultimately traced the cause to voltage instability rather than cyber interference, the event initially triggered widespread speculation of a cyberattack, underlining how technical failures and deliberate sabotage can appear indistinguishable in complex, interconnected grids.
- OT and ICS Intrusions Across Europe — According to the European Union Agency for Cybersecurity (ENISA), nearly one in five cyber incidents reported between mid-2024 and mid-2025 targeted operational technology systems. Pro-Russian hacker collectives such as Z-Pentest Alliance and NoName057(16) launched distributed denial-of-service (DDoS) and infiltration campaigns against industrial and energy-adjacent systems in Italy, Poland, and the Baltics — aiming to disrupt or intimidate essential infrastructure.
- Renewable Supply Chain Vulnerabilities (Germany, 2025) — Germany’s Federal Office for Information Security (BSI) warned of risks in internet-connected solar inverters, particularly imported models with weak encryption and remote-access backdoors. A large-scale compromise of such devices could theoretically destabilise local grids or serve as a botnet for coordinated cyberattacks.
- State-Linked Espionage and Supply Chain Compromise — Security researchers identified a Chinese state-aligned group, dubbed RedNovember, exploiting enterprise network equipment in several European countries, potentially providing access to energy sector systems through shared IT infrastructure.
- Academic Simulations of Energy System Exploitation — Research published in 2025 showed how clusters of distributed energy devices — such as domestic batteries or electric vehicle chargers — could be manipulated en masse to disrupt frequency stability. The Sherlock dataset project demonstrated how false data injection could deceive AI-based control systems, emphasising the need for resilient and explainable machine-learning defences.
Taken together, these incidents paint a picture of a sector increasingly under siege from both financially motivated criminals and state-aligned actors. Ransomware remains prevalent, but sophisticated campaigns targeting distributed renewables, supply chains, and control networks are becoming more frequent. The experiences of Electrica, HSE, and Bremanger highlight that resilience now depends not only on segmentation and rapid response but also on anticipating how adversaries might exploit Europe’s digitalised, AI-driven grids to cause real-world disruption.
Emerging Trends and Industry Insights
Broader data reinforces the scale of the threat. Spain reported a 43 per cent increase in cyberattacks on essential infrastructure in 2024, with the energy sector representing nearly one in ten incidents. In 2025, ENISA noted an escalation in state-aligned campaigns and hacktivist activity, often exploiting vulnerabilities in third-party software and distributed energy resources.
Research conducted by The Voice of Renewables supports these findings, indicating that more than half of European renewable energy operators surveyed had experienced at least one cyber incident in the past twelve months, with the majority citing phishing, ransomware, or unauthorised access through remote monitoring systems. The study also revealed that smaller operators — particularly those managing community solar and wind assets — were disproportionately affected due to limited cybersecurity budgets and reliance on outsourced IT support.
These developments underscore key lessons for Europe’s cybersecurity posture. First, segmentation and isolationbetween IT and OT networks remain critical to prevent lateral movement. Second, supply chain security must be prioritised, as compromised components — from inverter firmware to maintenance software — can serve as attack vectors. Third, rapid detection and response capabilities must be strengthened, as many operators still lack real-time monitoring and threat-hunting capacity. Moreover, edge assets such as home inverters, EV chargers, and demand response units should be treated as integral — and vulnerable — parts of the energy system.
Harnessing Technology for Defence
Technology can also be part of the solution. Secure digital twins can be used not only for operational optimisation but also for cyber-resilience testing, simulating attack scenarios before they occur. AI-driven analytics, if hardened against adversarial manipulation, can enhance anomaly detection and predictive defence. Blockchain-based systems may improve traceability and data integrity, offering tamper-proof audit trails in the event of an incident. Properly secured flexibility services can provide crucial buffers, allowing the grid to absorb disturbances and ensure quicker recovery.
A Call for Systemic Resilience
Strengthening Europe’s defences requires a holistic and forward-looking approach. Cybersecurity must be embedded into system design from the outset, following principles such as zero-trust architecture and least-privilege access. Mandatory certification schemes should ensure that every connected component — from smart meters to industrial controllers — meets stringent security standards. Cross-border collaboration, intelligence-sharing, and coordinated exercises must be expanded, alongside training initiatives that embed cybersecurity awareness into all layers of organisational culture.
The energy transition is as much a digital revolution as it is a decarbonisation effort. Europe’s energy security will depend not only on turbines and solar panels but also on encrypted data, resilient AI systems, and secure digital infrastructure. The surge of cyber incidents in 2025 serves as a warning: without robust defences, the very technologies enabling the clean energy transition could become its greatest vulnerability. By embedding cybersecurity into every facet of the energy ecosystem — from local devices to continental data spaces — Europe can ensure that its digital energy future is not only sustainable and innovative but also secure.